Reclaim Your Privacy.
Welcome to the Mailfence blog.
Mailfence News

Mailfence Release Notes March 2024
We’re happy to present the Mailfence Release Notes for March 2024 with several improvements and fixes. Release Notes: New Features Improvements The Mailfence Release Notes

Introducing Mailfence Base plan: Perfect for individuals and families
We’re thrilled to announce the launch of our latest subscription plan – the Mailfence Base Plan. This plan is tailored specifically to meet the needs
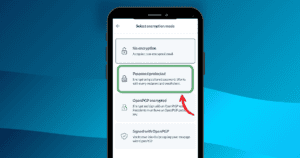
Introducing Encryption to our Mailfence Mobile App
We are very happy to announce that some major new features are now available in our Mailfence mobile app, including OpenPGP encryption, symmetric encryption, and
Email Security
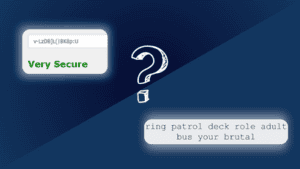
Password vs Passphrase: Which One Is Right For YOU? 🤔
A password vs a passphrase: do you know the difference? And more importantly, do you know when to use one or the other? Choosing the

How to Encrypt a File Like a Pro: 5 Easy Methods
Knowing how to encrypt a file is such an underrated skill to have. Not only does encrypting your files protect your sensitive data from cybersecurity

6 Essential GDPR Compliance Best Practices for Email Security – by Captain Compliance
Introduced in 2018, GDPR compliance is still something many companies battle with. More specifically, the handling of emails plays a vital role in digital privacy
Online Privacy

CSA Regulation Open Letter: NO to Client-Side Scanning!
Today, Mailfence and other privacy-first companies publish their Open Letter regarding the proposal for a regulation on Child Sexual Abuse (CSA). Here below is the

Secure File Transfer: 5 Killer Methods for Sharing Sensitive Files
Online secure file transfers have become an integral part of our daily lives. Important documents, photos, or videos… We share stuff over the Internet all

How to Dispose of Old Cell Phones: Safeguarding Your Secrets, Step by Step
Are you wondering how to dispose of old cell phones? Then you’ve come to the right place. In today’s digital age, smartphones have become an
Productivity

What is an Email Thread and When You Should Start One?
It’s effortless for your email inbox to get cluttered, making it hard to find a specific conversation or keep track of a topic. This is

How to Migrate your Skiff Account to Mailfence in 4 Easy Steps
Are you looking for a way to migrate your Skiff account? You are not the only one. On Feb 9th, Notion announced its purchase of

Email Greetings in 2024: The Best and Worst for Every Situation
Email greetings are your first opportunity to make a good impression on somebody. Did you know that making a great first impression when you meet
Emails and More.
An integrated suite of tools.